How To Create Fake Email Address Within Seconds
mail address is a type of identification by which an email receiver identifies the person who sends mail to him/her. That's why while creating an email address you need to enter your personal details that must be valid. However, what if we tell you that you can create an email address that doesn't require any validation of personal details and that email address gets permanently deleted after your work is done. So here we have a method To Create Fake Email Address. By this, you can create a fake email address that will get auto-deleted after ten minutes. Just follow the below steps to proceed.
Note: The method we are discussing is just for a known purpose and should not be used for any illegal purposes, as we will be not responsible for any wrongdoing.
How To Create Fake Email Address Within Seconds
The method of creating a fake email address is very simple and easy as these are based on online websites that will provide you a free email address without taking any personal details from you.
#1 10 Minute Mail
10 Minute Mail will provide you a temporary e-mail address. Any e-mails sent to that address will show automatically on the web page. You can read them, click on links, and even reply to them. The email address will expire after 10 minutes.
#2 GuerrillaMail
It is one of the most user-friendly ones out there, with this, you can get disposable email ID easily. You need to enter the details, and the fake email ID will be generated. Moreover, this also lets you send emails with attachment up to 150MB. You will be provided with a temporary email address which you can use to verify some websites which require the email address.
#3 Mailinator
Mailinator is a free, Public, Email System where you can use any inbox you want. You will be given a Mailinator address which you can use anytime a website asks for an email address. The public emails you will receive will be auto-deleted after few hours of receiving.
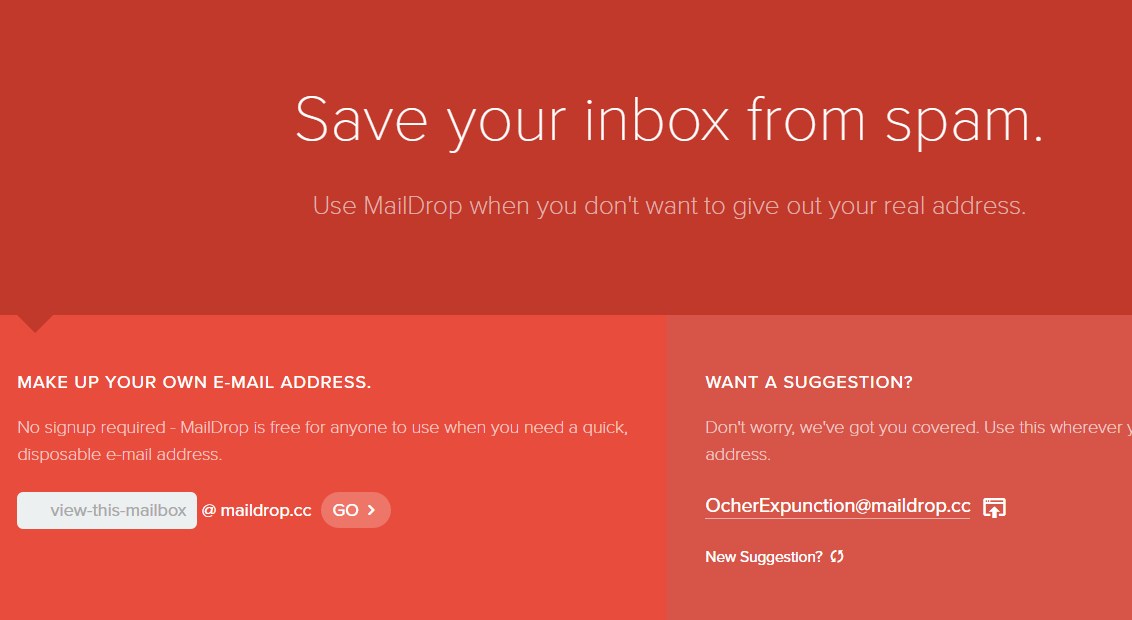
#4 MailDrop
Maildrop is a great idea when you want to sign up for a website but you are concerned that they might share your address with advertisers. MailDrop is powered by some of the spam filters created by Heluna, used in order to block almost all spam attempts before they even get to your MailDrop inbox. This works the same way like Mailinator in which you will be given a temporary Email address which you can use to verify sites etc.
#5 AirMail
AirMail is a free temporary email service, you are given a random email address you can use when registering to new websites or test-driving untrusted services. All emails received by AirMail servers are displayed automatically in your online browser inbox.
Related posts
- Pentest Tools
- Pentest Tools Review
- Hacker Tools Apk Download
- Hacking Tools For Windows 7
- Hacker Tools 2020
- Hack Tools Pc
- Hacking Tools For Mac
- Hacking App
- Pentest Tools Open Source
- Hacker Tools Apk
- Hack Tools
- Pentest Tools Github
- Hacking App
- Nsa Hack Tools Download
- Hacker Tool Kit
- Pentest Tools Apk
- Tools Used For Hacking
- Hacker Tools List
- Hackers Toolbox
- Hacker Tools Mac
- Hacking Tools 2020
- Pentest Tools Free
- Hackrf Tools
- Hacker Tools 2020
- Hack Tools Download
- Hacking Tools For Windows
- Kik Hack Tools
- Growth Hacker Tools
- Hacker Tools Mac
- Hacking Tools For Pc
- Black Hat Hacker Tools
- Pentest Tools For Android
- Hacker
- Hacking Tools And Software
- Hack Tools For Windows
- Pentest Tools Review
- Best Hacking Tools 2020
- Hack Tools 2019
- Computer Hacker
- Pentest Tools Nmap
- Hacking Tools For Kali Linux
- Growth Hacker Tools
- Hacker Tools Hardware
- Hacking Tools For Pc
- Hacker Tools 2020
- Usb Pentest Tools
- Hacker Tools Github
- Hack Tool Apk
- Hack Tools For Mac
- Hacker Security Tools
- Hack Tool Apk
- Hacking Tools 2019
- Hacker Tools List
- Hack Tools For Pc
- Game Hacking
- Hacker Tools Software
- Hacking Tools Windows 10